
Egyedi kiegészítések
Kiegészítőinkkel maximálisan vállalkozásához igazíthatja az SAP Business One rendszerét
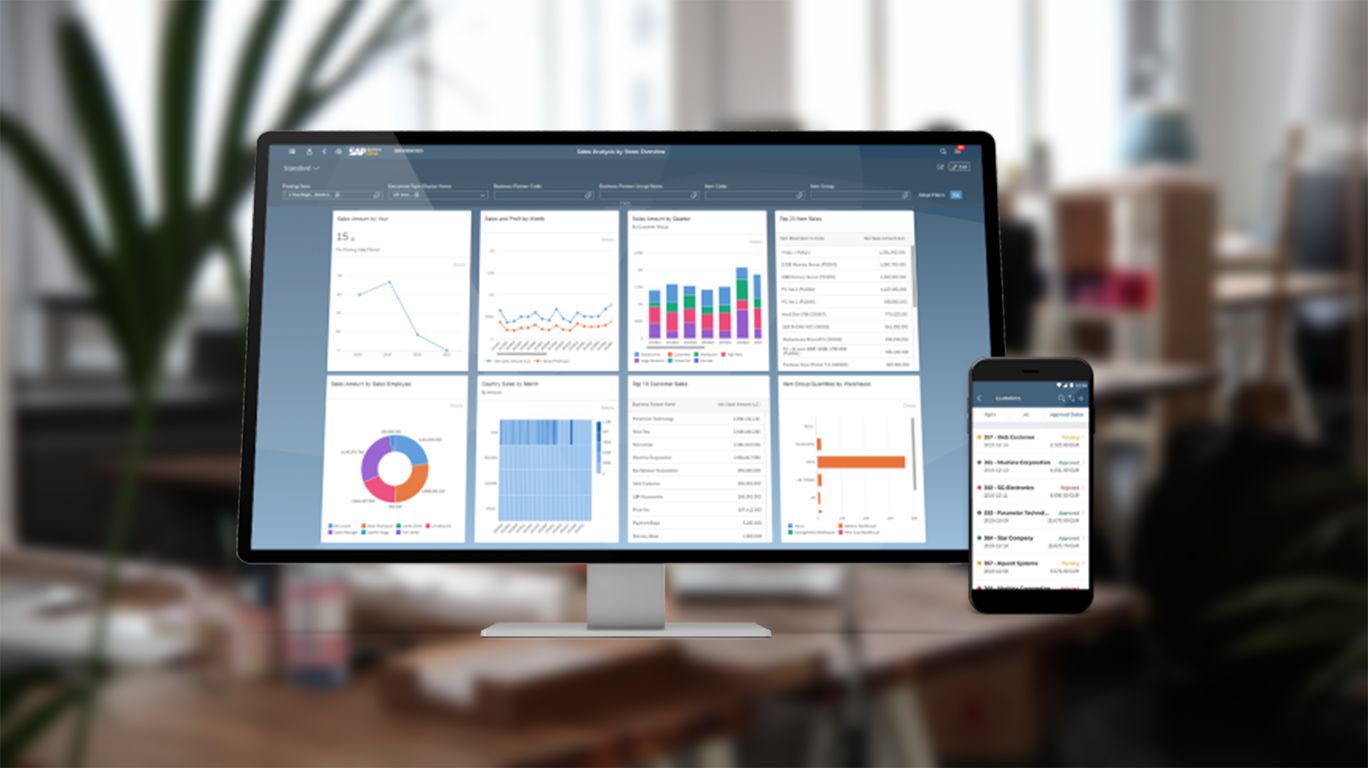
SAP Business One
Nagyvállalati szintű rendszer kis és középvállalkozások számára
Bemutatókérés
Tanácsadóink szívesen felkeresik Önt cége telephelyén, hogy bemutassák, termékeink miként javíthatják vállalkozása üzletvitelét